AWF5500
Virtual Web Application Firewall

Sorry, this product is no longer available, please contact us for a replacement.
Overview:
Array AWF Series WAF Appliances
Enterprise & Government
Enterprise and government Web sites and applications are increasingly the target of malicious attacks. Array's AWF Series WAF can protect against the most widespread attack mechanisms while providing active incident response to halt hackers in their tracks, with post-incident analysis and diagnosis to guide in strengthening servers against future attacks.
Cloud Providers
For Software-as-a-Service providers, the AWF Series protects the most vital business asset – the software applications that generate revenues – from malicious attacks, tampering and other security incidents. Infrastructure-as-a-Service providers can also leverage the AWF Series to offer WAF-as-a-Service for customers operating eCommerce sites and other Web assets in their cloud.
eCommerce Sites
Like enterprises and governments, eCommerce sites face a growing threat from Web site attacks and tampering, with the added danger of the loss of customer financial or other private information. Array's AWF Series protects eCommerce sites through a strong portfolio of tools such as continuous scanning, active incident response and post-incident analysis/diagnosis, and much more.
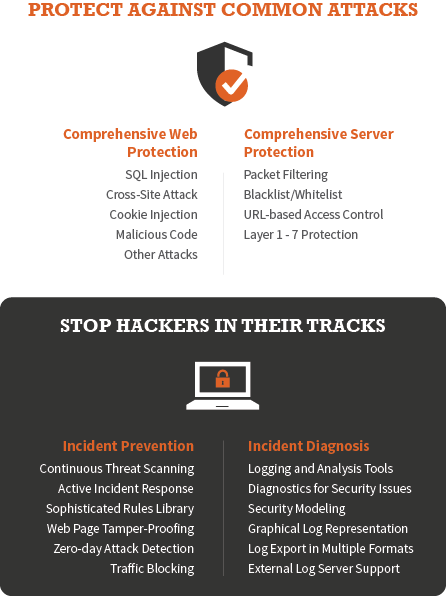
Comprehensive Protection
Continuous Threat Scanning
Array's Web application firewall continuously scans servers for known vulnerabilities, and scans applications for SQL injection or cross-site scripting vulnerabilities. In addition, a sophisticated rules library protects against a wide variety of Web server attacks, prevents inadvertent information disclosure, and protects and detects Web site embedded Trojans.
Strong Incident Response
During a security incident, the AWF Series effectively detects, blocks and prevents further intrusion, SQL injection, cross-site scripting and other types of Web application attacks. After a security incident, the AWF Series diagnoses for critical security issues such as Web site tampering and malicious code, allowing administrators to reduce security risk and maintain the Web servers' credibility.
Web Page Tamper-Proofing
Array's AWF Series Web application firewall (WAF) supports centralized management and control of all Web-page tamper-proofing endpoints, and provides content monitoring, synchronization and publishing functions while utilizing very few system resources. Page integrity of protected Web pages is checked before permitting end-users to access, thus preventing access to contaminated pages.
Comprehensive Server Protection
The AWF Series includes key network firewall features to provide comprehensive Layer 1 through 7 protection for Web application servers, including packet filtering, blacklist/whitelist, URL-based access control and other basic protection functions at the network layer.
Easy Configuration & Management
Guided Configuration
Configuration of Web application firewalls has been notoriously more complex than that of network-level firewalls. The AWF Series provides configuration guidance to assist administrators in accurately configuring and setting up the Web application firewall.
Visualized Management
The AWF Series' powerful equipment monitoring functions allow administrators to monitor – in real time – the associated equipment's working condition, attack threats and other system information, allowing timely discovery and elimination of network problems, and promoting stable operation.
Role-Based Authentication
The AWF Series supports three separate administration roles: administrator, account administrator and audit administrator. Using distinct roles can assist in meeting quality standards and the audit needs of regulatory and other requirements.
Highlights & Benefits
- Next-generation Web application firewall operates on multiple levels to protect vital Web servers and applications
- Continuous scanning for Web application vulnerabilities and for SQL injection or cross-site scripting and other threats within applications
- DDoS protection via brute force attacks mitigation
- Active incident response including detection, blocking and prevention of intrusion and other attacks, including zero-day detection by abnormal behavior analysis techniques
- Post-incident diagnosis and analysis of security issues to reduce overall security risk and maintain Web site credibility
- Highly refined rules library includes sophisticated protections such as information disclosure protection, embedded Trojan detection and protection, protocol integrity detection, keyword filtering and much more
- Comprehensive Layer 1 through 7 protection for Web servers at the network level, including packet-filtering, URL-based access control, blacklist/whitelist and other protection functions
- Web page tamper-proofing through centralized management and control of all Web tamperproofing endpoints, with content monitoring, synchronization and publish functions
- Customizable feature library and flexible configuration model to meet the needs of complex Web applications
- Comprehensive management portal provides visualized monitoring at the system, hardware, attack and tamper-proofing levels
- Guided configuration with exception rules to reduce installation complexity and errors
- Comprehensive management portal provides visualized monitoring at the system, hardware, attack and tamper-proofing levels
- Role-based authentication at the administrator level to secure configuration and data and allow for auditing
- Logging and log analysis with graphical representation and easy export of logs and statistics